
AI in Encryption Compliance Updates | Digital Fractal, Edmonton, AB
Encryption compliance is evolving rapidly in 2026, driven by stricter regulations, AI advancements, and growing accountability for businesses and executives. Here’s what you need to know:
- Global Regulations: New laws like Canada’s federal privacy law (replacing PIPEDA), Quebec’s Law 25, and the EU AI Act (effective August 2, 2026) introduce heavy fines – up to 5% of global revenue or €35 million. Non-compliance now holds executives personally accountable.
- Rising Costs: Companies spend over C$100,000 annually on audits, with compliance demands slowing IT modernization for 89% of businesses.
- AI Solutions: AI tools are transforming compliance with real-time monitoring, automated regulatory tracking, anomaly detection, and encryption key management. These systems reduce errors, speed up detection (from days to seconds), and cut manual tasks by 75%.
- Challenges: Businesses face hurdles like "Shadow AI", fragmented global regulations, and managing non-human identities like tokens and machine credentials.
Takeaway: AI-driven compliance is no longer optional. It ensures businesses stay ahead of regulations, reduce risks, and avoid costly penalties.
For Canadian companies, local providers like Digital Fractal Technologies deliver tailored AI solutions, automating compliance workflows and addressing unique industry needs. With 75% of organizations planning to adopt AI compliance tools by 2027, now is the time to act.
How AI Agents Cut Compliance from DAYS to MINUTES | Use Cases in Finance
AI Solutions for Monitoring Encryption Compliance
The challenges of managing encryption compliance today call for a shift in approach – from reactive to proactive. With fragmented regulations and the limitations of manual oversight, AI technologies now offer practical solutions to monitor encryption standards in real time. These tools not only reduce the workload for compliance teams but also improve accuracy. They focus on three key areas: keeping up with regulatory changes, spotting anomalies as they occur, and identifying weaknesses in existing protocols.
Automated Tracking of Regulatory Changes
Trying to manually stay on top of encryption regulations is becoming nearly impossible. Over the past decade, regulatory demands have surged by more than 200%, and violations can cost organisations an average of C$15 million each year. AI-powered platforms are stepping in, using Natural Language Processing (NLP) to scan regulator websites, legal databases, and official publications for updates to encryption standards and data protection laws [23–25]. With tools like NLP and knowledge graphs, these platforms can classify new regulations and link them to internal controls, cutting the time spent on manual updates by up to 90% [21, 23, 26].
To make things even easier, smart alert systems filter notifications based on terms like "cybersecurity" or "encryption", minimizing unnecessary alerts. For example, in early 2024, NextRoll adopted Relyance AI’s compliance platform and saw a staggering 1,660% improvement in the visibility of its data processing activities within just three weeks. With the global AI compliance monitoring market expected to grow from C$1.8 billion in 2024 to C$5.2 billion by 2030, it’s clear that AI is reshaping how organisations manage compliance. Beyond just tracking updates, AI is also equipped to detect deviations in real time, which brings us to anomaly detection.
Real-Time Anomaly Detection
Traditional compliance monitoring often relies on periodic audits, which can take days to uncover breaches – four to seven days, on average. AI changes the game by learning "normal" patterns of data access and transmission. It flags anything unusual, like unauthorized data transfers or suspicious access attempts, almost instantly. With AI, the detection time drops from an average of 5.2 days to a mere eight seconds – a mind-blowing 99.998% improvement in speed. This real-time detection can stop up to 94.4% of compliance violations before they even happen.
Advanced tools like runtime gateways and algorithmic policy engines evaluate data requests on the spot, ensuring they comply with pre-set rules ("policy-as-code") and blocking or redacting non-compliant actions. AI-driven solutions like Data Detection and Response (DDR) and Data Security Posture Management (DSPM) offer continuous oversight of data flows, keeping tabs on how sensitive information moves through systems and databases. For example, these tools can catch risks like sensitive data stored in publicly accessible cloud spaces linked to AI models – something traditional monitoring might overlook. A case in point: in 2025, SecureBank used AI to monitor transactions and automate regulatory reporting. The results? A 95% compliance rate, an 80% drop in operational risk, and 99.9% accuracy in flagged transactions.
Gap Analysis for Protocol Compliance
AI doesn’t stop at updates and anomalies – it also helps organisations pinpoint weaknesses in their encryption protocols. By analysing frameworks like GDPR and NIST, AI tools can score internal systems and highlight gaps, such as missing integrity checks for individual messages.
On average, organisations deal with 234 regulatory events daily across 190 countries. Yet, 60% of Governance, Risk, and Compliance (GRC) users still rely on error-prone spreadsheets to manage compliance. AI-powered tools can reduce compliance-related incidents by 40%. These advanced systems also detect "control drift" in real time, alerting teams when encryption settings change or fail to meet standards. When gaps are identified, AI provides actionable recommendations – like adopting specific encryption measures or securing access paths to critical systems. Some platforms even include "crosswalk" features, allowing teams to map evidence once and apply it across multiple frameworks (ISO, SOC, HIPAA, PCI), cutting down on redundant work.
"AI is creating and moving data faster than any team can track. Only AI-native tools like Relyance can keep up with the discovery and enforcement loop." – Chris Bender, CISO, ClickUp
Using AI to Improve Encryption Key Management
Managing encryption keys manually has become increasingly unsustainable as systems grow more complex. Traditional methods fail in 73% of cases because manual processes simply can’t keep up with the demands of distributed environments. AI is changing the game by automating the entire lifecycle of encryption keys – from creation and rotation to eventual retirement – while ensuring real-time compliance monitoring.
Automated Key Lifecycle Management
With real-time anomaly detection bolstering compliance efforts, effective key management is more critical than ever. AI-driven systems take over the heavy lifting, automating tasks like key rotation, issuance, and expiration. This eliminates risks tied to expired certificates or inconsistent policies. By analysing usage patterns, these systems determine the best rotation intervals and flag anomalies that could indicate compromised keys. For organisations preparing for post-quantum cryptography, this automation supports "crypto-agility", enabling fast adaptation to new encryption algorithms and frequent key rotations without manual intervention.
Modern platforms, such as Google Cloud KMS Autokey, streamline this process further. They automatically provision keys, assign them, and enforce role-based access controls while maintaining hardware security module (HSM) protection. These platforms can even support daily key rotations. For organisations managing thousands of keys across Kubernetes clusters and CI/CD pipelines, automation is essential to scaling operations. Compliance standards like PCI-DSS 4.0 now require regular key rotation for sensitive data, making automation a necessity.
"Manual key rotation introduces risk, especially in setups with multiple participants… That’s why automated key rotation – via a secure and centralised system – is critical." – Raidiam
When implementing automated rotation, it’s important to keep old keys in an "enabled" state temporarily to decrypt in-progress tokens or existing data. JSON Web Key Sets (JWKS) are useful for publishing updated public keys in a standardised format. Since rotation doesn’t automatically update existing ciphertext, systems should include automated processes for decrypting older data and re-encrypting it with the current key. Beyond rotation, AI enhances security by creating immutable audit trails for every cryptographic action.
AI-Driven Audit Trails and Reporting
AI systems provide detailed tracking of every encryption-related action, creating structured, tamper-resistant records that meet regulatory requirements. These audit trails document everything – from the rationale behind encryption decisions to system states and model versions – ensuring transparency and accountability. To prevent tampering, logs are cryptographically verified and stored in append-only formats, preserving data lineage.
For example, in early 2026, a Chief Compliance Officer at a European tech company used FireTail‘s centralised AI audit trails to respond to a complex GDPR data access request in minutes, a task that previously took days. Similarly, in January 2026, Synthesia deployed Wiz‘s AI Security Posture Management (AI-SPM), which provided prioritised alerts that helped engineers quickly address vulnerabilities in their AI infrastructure.
AI also monitors logs and system communications in real time to catch issues like unauthorised decryption attempts, excessive key usage, or encryption bypasses – problems that manual systems often miss. By 2026, half of the world’s governments expect enterprises to comply with specific AI and data privacy laws, making these capabilities essential. To ensure auditability, adopt structured logging formats with consistent schemas rather than relying on free-text logs.
Policy Alignment for Data-at-Rest and Data-in-Transit
AI tools simplify regulatory compliance by translating complex rules into machine-readable code, ensuring encryption policies are applied consistently across all data states. Data Security Posture Management (DSPM) acts as a unified intelligence layer, discovering and classifying sensitive data across hybrid multi-cloud environments. It tracks data at rest and maps its movement in transit.
By enforcing encryption policies across cloud platforms, endpoints, and applications simultaneously, AI eliminates configuration drift and ensures no gaps exist between stored and transmitted data. These systems also adjust encryption strength dynamically based on real-time factors like user behaviour, device trust, and location. AI even traces data lineage through SQL parsing and API monitoring, tracking how data moves through workflows from storage to active use in AI models or databases.
"AI-powered encryption refers to using machine learning and automation to… adapt encryption policies dynamically [and] eliminate gaps caused by manual configuration drift." – Mindcore Technologies
To maintain control, use Policy Decision Points (to decide if an action is allowed) and Policy Enforcement Points (to carry out those decisions). Anchor encryption choices to verified identities and device trust rather than relying solely on network perimeters. AI agents can also mask or anonymise sensitive fields when data is accessed by non-privileged users or moved into lower-security environments, ensuring continuous compliance.
sbb-itb-fd1fcab
Digital Fractal Technologies‘ Role in Encryption Compliance
Meeting encryption compliance isn’t a one-size-fits-all task – it requires solutions tailored to specific operational needs. Digital Fractal Technologies, with over two decades of experience, specializes in creating custom applications that address the unique compliance challenges faced by Canadian businesses. This expertise is particularly valuable in industries like energy, construction, and the public sector. Their AI-driven monitoring tools, previously discussed, gain practical application through Digital Fractal’s focus on compliance automation.
Custom Software for Protocol Monitoring
Digital Fractal develops monitoring systems that seamlessly integrate into existing enterprise frameworks while ensuring data sovereignty and accountability. By leveraging SOAR (Security Orchestration, Automation, and Response) and XDR (Extended Detection and Response) capabilities, they automate threat detection and enable 24/7 monitoring. These systems are particularly beneficial for high-stakes industries, where specialized AI agents handle tasks like verifying safety forms, regulatory documentation, and equipment logs in real time. For example, their Compliance Agents and HSE Safety Agents streamline processes that were traditionally manual.
In 2020, Digital Fractal revolutionized Xtreme Oilfield‘s operations by digitizing paper-based workflows and automating permit management. Regg. M from Operations shared:
"Digital Fractal Technologies was contracted to digitally transform our trucking operations… digitized our paper forms, automated certificate/permit management, computerized job dispatching, and brought timesheets, vehicle repair and communications to the field on an iPad".
By replacing manual tracking with automated compliance monitoring, they eliminated gaps in documentation and reduced the risk of human error. This approach naturally supports continuous updates to compliance workflows, ensuring businesses stay ahead of regulatory requirements.
Workflow Automation for Compliance Updates
Digital Fractal enhances existing systems by adding intelligent automation rather than starting from scratch. Their AI layer integrates into current mobile and web applications, automating data extraction and enabling proactive decision-making. This streamlines repetitive tasks, saving both time and money, and allows businesses to transform their operations within just 90 days.
Justin N, a manager who collaborated with Digital Fractal, noted:
"What impressed me the most with Digital Fractal is when issues arose, not only were they diagnosed in a timely fashion, but they also executed on solutions that ensured we would never encounter the same problem twice – future proofing our technology".
This forward-thinking approach ensures encryption policies stay up-to-date as regulations evolve, reducing the need for constant manual intervention.
Scalable Tools for Regulatory Adherence
To tackle ongoing compliance challenges, Digital Fractal employs scalable AI tools designed to adapt to shifting regulatory landscapes. One of their standout offerings is the 30-day AI Readiness Audit, priced between $2,500 and $10,000 depending on scope. These audits identify compliance gaps and provide a detailed roadmap for implementing automation systems over a 6–12 month period. Deliverables include a written report, slide deck, strategic roadmap, and a prioritized list of automation opportunities. By offering enterprise-grade protection to small and medium-sized businesses, they ensure robust compliance without straining resources.
With a technical team that includes AI and big data experts – some holding doctorates – and a portfolio of over 120 completed projects for more than 100 clients, Digital Fractal delivers the expertise required for navigating complex compliance landscapes. Their global presence, with offices in Edmonton, Alberta, as well as the USA, Tunisia, and Vietnam, allows them to provide localized solutions while maintaining consistent adherence to regulations across different regions.
Benefits of AI in Encryption Compliance and Next Steps
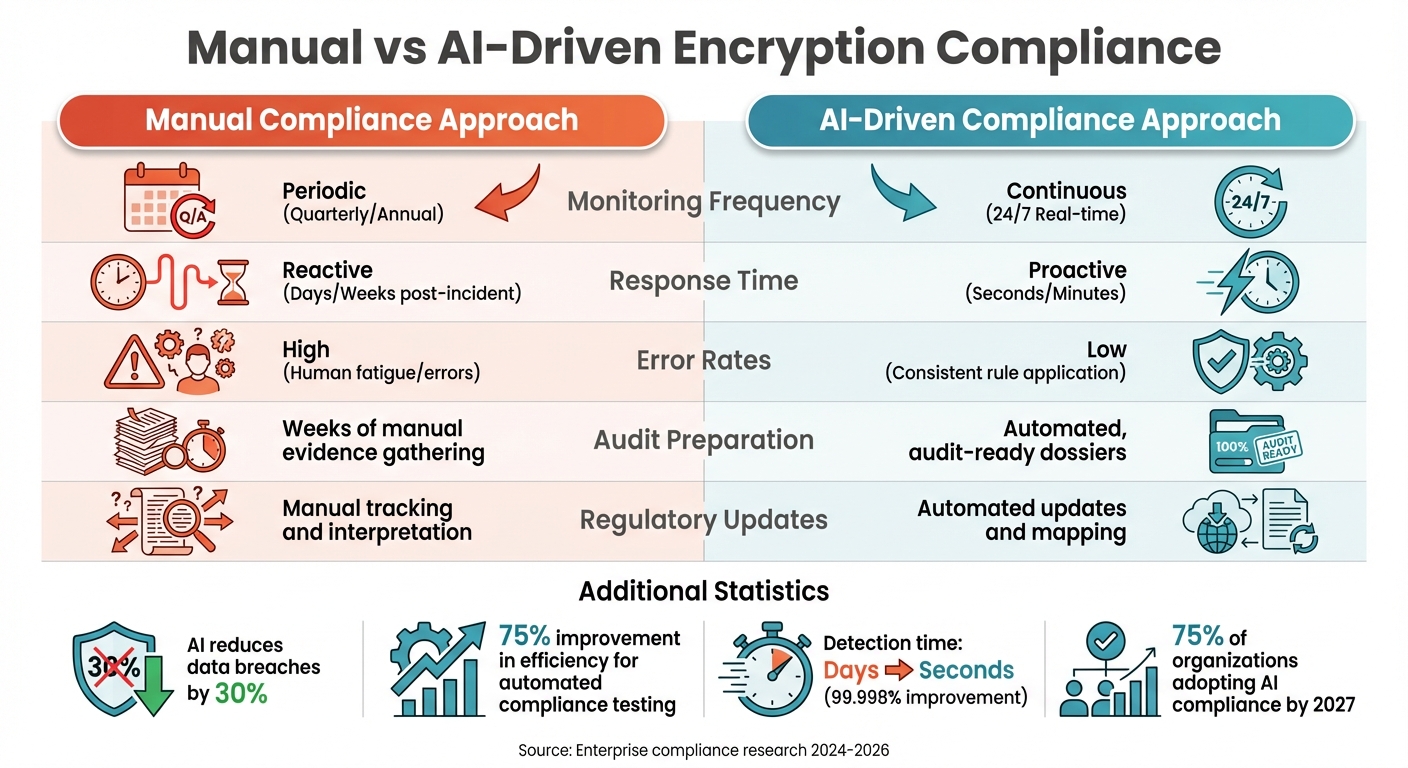
Manual vs AI-Driven Encryption Compliance: Key Differences
Key Advantages of AI in Compliance
AI has transformed encryption compliance from a reactive process into a proactive and dynamic tool. For example, AI-driven security measures have been shown to reduce data breaches by 30% and cut down security incidents in 63% of cases. According to a study by Forrester, companies using integrated GRC (Governance, Risk, and Compliance) software avoided $1.4 million in regulatory fines and reputational damage.
By automating repetitive tasks like manual document reviews and ticket routing, AI-enhanced compliance testing improves efficiency by 75%. Additionally, AI enables continuous, real-time oversight, identifying breaches in seconds rather than days. This shift from periodic audits to constant monitoring allows businesses to address vulnerabilities before they escalate, which is vital considering the average data breach now costs $4.24 million.
| Feature | Manual Compliance Approach | AI-Driven Compliance Approach |
|---|---|---|
| Monitoring Frequency | Periodic (Quarterly/Annual) | Continuous (24/7 Real-time) |
| Response Time | Reactive (Days/Weeks post-incident) | Proactive (Seconds/Minutes) |
| Error Rates | High (Human fatigue/errors) | Low (Consistent rule application) |
| Audit Preparation | Weeks of manual evidence gathering | Automated, audit-ready dossiers |
| Regulatory Updates | Manual tracking and interpretation | Automated updates and mapping |
These advantages highlight how AI can significantly streamline compliance processes, laying the groundwork for a phased approach to AI adoption.
Implementation Strategies for Businesses
To fully leverage these benefits, organisations should adopt a phased and targeted strategy rather than attempting an immediate, large-scale transformation. Start by focusing on high-volume, repetitive tasks that involve manageable risk. Begin with a detailed data inventory, mapping the flow of sensitive information, storage locations, and third-party integrations to identify vulnerabilities.
For Canadian businesses, a 90-day structured implementation plan is a practical way to begin:
- First 30 days: Assign a governance team and inventory AI-enabled workflows.
- Next 30 days: Draft an AI Acceptable Use Policy and conduct a Data Privacy Impact Assessment for the highest-risk use case.
- Final 30 days: Map data flows and create a vendor-risk register.
This phased approach helps minimise disruptions while building robust compliance capabilities through expert AI insights.
To ensure data security, store encryption keys separately from data using Hardware Security Modules (HSMs) or cloud-based Key Management Services (KMS). Additionally, choose AI tools that provide clear audit trails and can justify their decisions to regulators – an approach that 73% of organisations now prioritise in their governance frameworks. As Certa puts it:
"AI systems need to be transparent and explainable, enabling organizations to understand, audit, and justify AI-driven decisions for compliance purposes".
Conclusion: Staying Ahead in Encryption Compliance
With 75% of organisations planning to implement AI-driven compliance solutions by 2027, delaying adoption could leave businesses vulnerable, especially as AI-powered attacks are expected to rise by 20% annually. Successfully navigating this evolving landscape requires a balance between automation and human oversight.
For instance, nearly 80% of lawyers now use AI tools in their workflows, yet they still rely on human verification due to generative AI’s hallucination rate, which ranges from 3% to 27% when summarising facts. The most effective approach combines the speed and precision of AI with the judgement and expertise of professionals, ensuring accountability and clarity in compliance decisions. By doing so, businesses can turn compliance from a financial burden into a strategic advantage.
FAQs
What 2026 rules are likely to change our encryption requirements?
The anticipated 2026 regulations are set to bring significant changes to encryption requirements, particularly with proposed amendments to the HIPAA Security Rule. These amendments aim to enforce stricter encryption protocols for electronic protected health information (ePHI), require the use of multi-factor authentication (MFA), and demand more rigorous oversight of vendors handling sensitive data.
Beyond HIPAA, global cybersecurity and AI compliance regulations evolving in 2026 are also influencing encryption standards across various industries. These changes are expected to be finalized by May 2026, marking a pivotal shift in data protection practices.
What data and systems should we monitor first with AI for compliance?
To keep compliance monitoring on track, focus on safeguarding sensitive data such as personally identifiable information (PII), financial records, and health information. These types of data are heavily regulated and come with higher risks if mishandled. Additionally, keep a close eye on critical systems like transaction platforms and access controls, as they play a key role in maintaining compliance standards.
Leveraging AI can make this process much more efficient. AI tools can handle tasks like automating oversight, spotting anomalies, and flagging potential violations. This not only helps organizations stay compliant but also allows them to address potential problems before they escalate.
How do we control “Shadow AI” without slowing teams down?
To keep "Shadow AI" in check without slowing down your team, focus on governance strategies that balance oversight with flexibility. Tools like real-time monitoring, drift alerts, and audit logs can help you stay on top of AI usage and flag any unauthorised activities.
Incorporating automated governance solutions into your workflows is another smart move. These tools can dynamically enforce policies, reducing risks such as data leaks, while still giving your team room to innovate. By doing this, you maintain compliance without putting unnecessary hurdles in the way of productivity.

